In today's digital landscape, domain names serve as the gateways to our online world. However, lurking beneath these seemingly innocuous addresses can be a plethora of hidden threats. Malicious actors are constantly devising innovative methods to exploit domains for nefarious purposes, ranging from phishing attacks and malware distribution to data breaches and identity theft. A comprehensive domain scan is essential for identifying and mitigating these risks, providing organizations with a critical layer of security.
- An in-depth domain analysis will delve into the technical intricacies of a domain, exposing security gaps.
- By investigating various factors such as DNS records, WHOIS information, and website content, security professionals can pinpoint threats.
- Such a strategic assessment helps organizations to strengthen their defenses, protect sensitive data, and maintain the integrity of their online presence.
Vulnerability Assessment: Proactive Security for Your Digital Assets
In today's rapidly evolving threat landscape, safeguarding your valuable information is paramount. A thorough Data Breach Scan provides you with a proactive approach to identifying potential vulnerabilities before malicious actors can exploit them. This process involves a deep dive into your infrastructure, meticulously examining every layer for weaknesses that could be leveraged by attackers. By proactively uncovering these vulnerabilities, you can take swift and targeted steps to mitigate the risk of a data breach and protect your organization from significant financial, reputational, and operational damage.
- Regularly conducting Data Breach Scans allows you to stay ahead of evolving threats and maintain a strong security posture.
- A thorough scan provides detailed reports that pinpoint specific vulnerabilities and offer actionable strategies for remediation.
- Committing in Data Breach Scans is an essential component of a robust cybersecurity strategy, demonstrating your commitment to protecting your organization's most valuable assets.
Digital Detox
In today's hyper-connected world, reclaiming your privacy online is more crucial than ever. The constant deluge of data collection, targeted advertising, and monitoring can feel overwhelming. However, there are steps you can take to regain control over your digital footprint. Think about internet removal as a powerful tool to break the ties that bind you to here the ever-present digital landscape. By limiting your online activity, you can create space for more meaningful experiences offline.
- Pros of internet removal include reduced stress, improved sleep, and a renewed focus on real-world relationships.
- It allows you to possess your time and energy, freeing yourself from the constant notifications and distractions that plague our digital lives.
- Utilize a mindful approach to technology by consciously choosing when and how you engage online.
While the prospect of internet removal may seem daunting, remember that it is a journey, not a destination. Start by setting realistic goals and gradually decrease your online time. Explore alternative activities that bring you joy and fulfillment offline.
Erase Your Digital Footprint
In today's hyper-connected world, our digital footprint can feel like an inescapable shadow. Every click leaves a trace, building a detailed profile that can be accessed by employers. If you're concerned about the amount of information readily available about you online, Ditch Your Online History might just be your solution. This service aims to remove your personal records from popular websites, giving you a fighting chance to reclaim some control over your online presence.
Nevertheless, it's important to understand that DeleteMe doesn't offer a complete solution. Some records may be impossible to delete. Still, for those wanting to minimize their digital footprint and secure some privacy, DeleteMe offers a valuable tool.
In-depth Domain & Data Leak Analysis
A robust approach to domain and data leak analysis is essential for reducing the risk of vulnerabilities. This entails a systematic examination of both external factors to uncover potential weaknesses and hazards. By executing a thorough analysis, organizations can efficiently address vulnerabilities before they are abused by malicious actors. A effective analysis will often harness a variety of methodologies to gather relevant data and analyze it for potential indicators of a leak.
Secure Your Presence: Domain, Data, and Internet Reputation Management
In today's digital landscape, establishing a solid online presence is paramount for any organization. This involves preserving your domain name, controlling your data effectively, and enhancing a positive internet reputation.
A reinforced domain is the foundation of your online identity. Regularly updating your domain registration and utilizing strong security measures can minimize the risk of attacks.
Utilizing your data responsibly is essential. This includes gathering data transparently and implementing robust privacy protocols to secure it from unauthorized access or leakage.
Furthermore, cultivating a positive internet reputation requires strategic efforts. This can involve engaging in online forums, publishing valuable content, and observing your online presence.
By emphasizing on these key areas — domain security, data management, and internet reputation management — you can establish a strong online presence that propels your growth.
 Jonathan Taylor Thomas Then & Now!
Jonathan Taylor Thomas Then & Now! Luke Perry Then & Now!
Luke Perry Then & Now!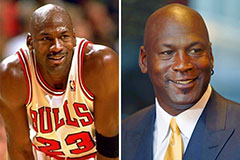 Michael Jordan Then & Now!
Michael Jordan Then & Now! Mike Vitar Then & Now!
Mike Vitar Then & Now! Jaclyn Smith Then & Now!
Jaclyn Smith Then & Now!